In Part 1 of this series, we provided an overview of Security Tokens. Specifically, we discussed the definition of a security, how Security Token Offerings (STO) are different from ICOs, their benefits, and the existing Security Token Ecosystem.
In Part 2, we have picked up Top 5 Projects which we deem future game-changers.
5. Securrency
Securrency is a platform that supports secure, compliant, and convenient issuance and trading of security tokens. The company creates interoperability among blockchains and legacy systems with associated Distributed Investment Banking Services (DIBS). Founded in 2015, Washington DC, It has an office in Abu Dhabi, UAE.
Notable features of the platform include:
- User-friendliness of the platform: Securrency makes it easier to issue tokens. The entire process is drag-and-drop-based and can be completed with a single click. The dashboard is customizable. It has different functions, such as an issuance portal or a full-service investment bank.
- Compliance: The software platform RegTex helps users comply with securities and digital currency transactions.
- Interoperability: The infrastructure is supported by the interoperability layer called the InfinExchange. Securrency has integrated with existing legacy systems to provide a multi ledger approach. Expected to come out in 2019, their push-and-pull infrastructure technology has integrated existing financial instruments. It was present on the market before the creation of the blockchain.
- Liquidity: Securrency promotes the “network effect” expansion of global liquidity. It achieves so by developing and deploying its core financial services infrastructure technology through global strategic partnerships. These partnerships are with legacy financial industry leaders and emerging leaders in the cryptocurrency community.
- CAT-20 Standards: Securrency has introduced the Compliance Aware Token (CAT-20 and CAT-721) standards. It is the world’s first truly interoperable ledger-agnostic security token protocol. Security tokens minted with the CAT protocols are self-governing and ensure compliance throughout their life-cycle using Securrency’s innovative regulatory technology.
4. Harbor
Launched in 2018, Harbor’s mission is to power the future of crypto-securities. For this, it wants to build a decentralized compliance protocol that standardizes the way securities are issued and traded on blockchains. The platform streamlines the alternative investment experience for investors, issuers and their placement agents. It unlocks liquidity options for traditionally illiquid assets.
Notable features include:
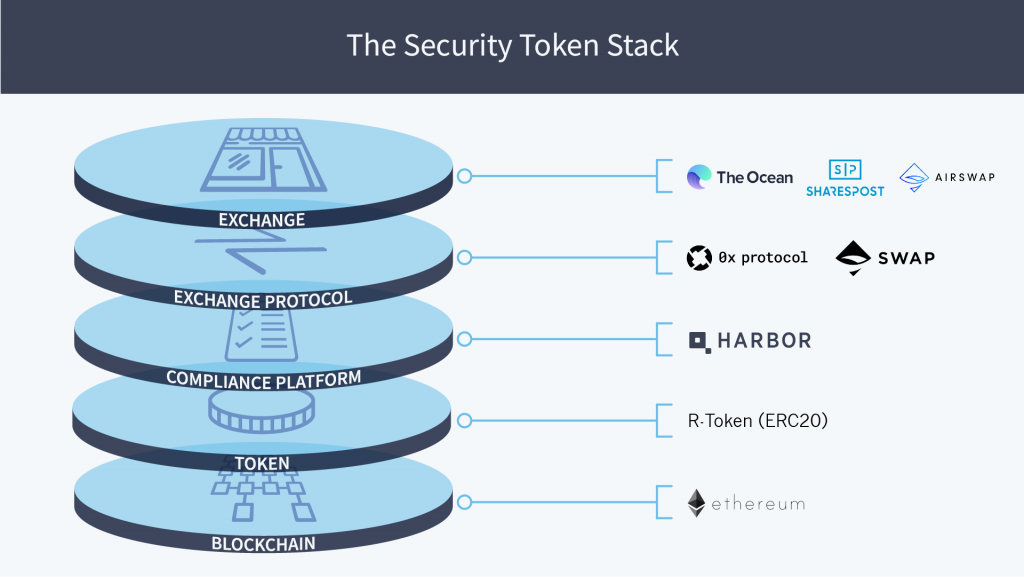
- Security Token Stack: Security Token Stack is a technology stack and an ecosystem — a network of on-chain smart contracts and off-chain processes. It works together to create a holistic solution for issuing, trading, and auditing securities using the blockchain as a store of value.
- R-Token: Harbor built the R-Token (an ERC-20 compatible token), as a core primitive of its compliance platform, to ensure compliance from initial offering through secondary trades. The security token does upfront checks using the whitelist provided by the compliance platform to ensure that all transactions occur within the required guidelines.
- Compliance Platform: The compliance platform bridges the on-chain and off-chain worlds throughout the lifecycle of the offering by publishing the result of off-chain processes to the on-chain whitelist. Elements of the compliance platform include the trade controller, issuance platform, policies and procedures, secondary trading, and testing/auditing.
- Interoperability: Harbor is chain agnostic, but it started with the Ethereum chain because it is programmer-friendly, has market penetration and has the largest ecosystem of wallets, exchanges and related services.
- Partnerships with exchange protocols: Partnerships with exchange protocols like 0x and Swap provide an essential layer to ensure a global liquidity pool. The decentralized protocols lower the cost of trading, remove barriers for overseas investors, and enhance security as it is not a centralized third party that holds funds or securities.
- Exchanges: R-Token can ensure securities trade only on properly licensed exchanges, like The Ocean, Sharespost, etc.
3. Swarm
Swarm is a non-profit foundation dedicated to building an open infrastructure for the new, emerging digital securities economy. It is a protocol that is offering tools to support the digitization of assets or other things of value. It ensures the establishment of compliance mechanisms and make the interfaces and infrastructure accessible and open to all. Swarm’s 3 primary pillars are Tokenization, Compliance, and Governance.
Notable features include:
- Digital securities: SWARM’s tokenization infrastructure is an open, full-stack solution for the life-cycle management of a Security Token Offering (STO). Token creation, configuration, fundraising, and issuance are easy and free. Swarm enables issuers to manage post-distribution activities such as token redemption, dividend issuance, asset governance, investor administration, reporting, and communications seamlessly.
- Market Access Protocol: Market Access Protocol (MAP) is a security token protocol focused on interoperability and designed to solve existing inefficiencies and difficulties encountered by token issuers, investors, exchanges, and qualification providers while preserving privacy. MAP is designed to facilitate this across multiple blockchains, and for all tokens – including security tokens issued via platforms other than SWARM.
- SWARM Masternodes: Owned and operated by the global community, SWARM Masternodes ensure the path for secure, trusted network infrastructure. Masternodes make SWARM and MAP work.
- Swarm provides SRC20 protocol, a cryptographic standard for security tokens to tokenize assets. Tokenized objects include real estates, renewables, agriculture, tech companies, crypto hedge funds, etc., that become “assets” that can be easily managed, governed and traded.
Here are some things that SRC20 security tokens enable:
- represent ownership of part of an object or “asset”
- allow holders to manage that asset through voting
- secure a right to any revenue streams from the asset
- are tradable in a regulatory compliant manner
- Swarm has its native token called SWM to facilitate economic activities on the Swarm platform.
Swarm blockchain was built on a custom fork of Stellar. It has since extended the security token framework into other chains, starting with Ethereum, and the infrastructure is now blockchain agnostic.
2. TZero
tZero grew out of an earlier effort by Overstock.com, the online retailer, to develop a blockchain technology called Medici. Medici was designed to allow Overstock, as well as other businesses that license the technology, to be able to sell cryptocurrencies. It is currently headed by Sam Noursalehi, who was a former president and board member of Overstock.com
tZero exchange is considered as an alternative trading system (ATS) and is regulated by the Securities and Exchange Commission.
Notable features include:
- Proprietary Technology: Using proprietary blockchain technology and strategic partnerships, tZERO is presenting an innovative capital markets platform.
- Pooling: It is creating a two-sided network connecting issuers with investors in a superior solution for accessing capital and enabling secondary liquidity for traditionally illiquid investments. The platform’s design allows buyers and sellers to trade through a dark pool, which means that it will act as a matchmaker rather than a broker. A distributed ledger allows to manage transactions.
- Speed: By designing and building its trade and settlement processes on a public blockchain, tZERO’s platform reduces the trade settlement cycle from T+2 to same-day settlement (T+0 or simply T0).
- Additional advantages of this alternative system include democratized access, enhanced transparency, and an increase in overall efficiency.
- Regulation: tZero enjoys a substantial advantage when it comes to financial products based on cryptocurrencies, as it can provide services that other platforms may not be able to provide.
- Other possible offerings: Because it is required to comply with regulations, tZero can position itself as a provider of advice, clearing, and verification services to other companies looking to release tokens to raise funds.
On January 10, 2019, tZERO launched the technology necessary for its, wholly-owned, broker-dealer subsidiary, PRO Securities, LLC (PRO) to operate its revolutionary security token trading platform. The platform, which is now active and currently accessible only to accredited investors, enables trading and settlement of security tokens on the Ethereum blockchain.
1. Polymath
Polymath Network (Polymath) is a decentralized protocol-plus-platform that facilitates the creation of security tokens. The platform aims to bring the multi-trillion dollar financial securities market to the blockchain. In 2017, following a highly successful ICO, Polymath launched its services.
Notable features include:
- Platform:
- Polymath’s global platform provides legal and technical solutions for securitizing bonds, stocks and other assets on a blockchain.
- It is a self-serve platform – security token issuers can use the Polymath Token Studio to create a security token in 10 minutes
- Besides, token issuers can also contact securities law firms, broker-dealers, KYC/AML providers, marketing firms, and custody providers for help with their security token creation and security token offering. However, these parts of the process, from drafting documents to fundraising, can take weeks or months.
- ST-20 Standard: Polymath has its own ST-20 token standard for it and also their native smart contracts. It’s through ST-20 token, Polymath is working to improve interoperability and hence, increase adoption.
- Compliance:
- KYC and AML(Anti Money Laundering): Securities cannot be sold to someone without knowing who they are, their appetite for financial risk, and their source of funds. Polymath platform integrates with a number of KYC/AML providers that will check the identity, residency, and accreditation status of every individual who wants to potentially invest in such a token. Hence, only authorized investors are able to transact with security tokens.
- Locational blocks exist. They prevent participation of residents from banned countries.
- The Polymath protocol allows issuers to enforce these checks and restrictions for both the primary issuance and secondary trading. If you trade ST-20 tokens on a secondary exchange, the compliance checks still take place prior to every token transfer. This ensures that the KYC provider of the issuing entities’ choice vets the recipient.
This gives issuers the peace of mind they need to safely issue blockchain-based securities. And provides investors with the assurance that they are subject to protection under securities laws.
Even more
- Partnerships: Polymath has industry partnerships with the likes of tZero that will provide the much-needed liquidity for the security tokens launched on Polymath blockchain.
- POLY: Polymath’s own native token. Users utilize it as an economic unit for all the operations on the Polymath’s blockchain.
- Polymesh: Polymesh is an initiative to build a purpose-built security token blockchain. The goal of the Polymesh blockchain initiative is to provide an infrastructure that addresses the needs of institutions. Concurrently, it also aims to empower participants to invest and create their own security tokens.
Conclusion:
The main challenges faced by the security token industry are education, adoption, and interoperability. All in all, we can conclude that despite the challenges encountered by the platforms and exchanges addressed in this feature, the adoption, even if slow, is imminent.
Even if security tokens don’t disrupt the world of finance as ICOs did, they will definitely transform the way we raise and invest in money.
Join us on Telegram to receive free trading signals.
For more cryptocurrency news, check out the Altcoin Buzz YouTube channel.































Polymath never had an ico, you should edit that out
Hi James! Thanks for the comment. Regarding Polymath: it did have an ICO. Please check out this link: https://icodrops.com/polymath/
Hope you enjoyed the article!
They had an ICO – which I have no issue with. What I do have an issue is that they spent all the money on a party, which is still going. How they are are top? Come on. ?
How about Smartland (SLT)? Is it good? Any comments?