There’s never been a better time to stay security conscious than now when crypto is going mainstream. Large institutions like BlackRock, Fidelity, JP Morgan, and Microsoft aren’t the only ones with an interest in crypto. Seasoned scammers also want a piece of the pie.
Crypto hacks and scams have increased over the past couple of years. In 2023 alone, more than $1 billion was lost to hackers, and a recent report suggests that these hackers are constantly on the lookout for sophisticated ways to carry out their craft.
A New Type of Scam
One of their recent tactics making the rounds on Telegram allows the hacker to empty the user’s wallets without the victim needing to confirm any transaction. However, this kind of attack only affects tokens that comply with the ERC-2612 token standard.
Hi guys I’m new to crypto and I just lost everything by connecting my wallet to the Syncus telegram group they said that I need to connect my wallet to a web3 to stake and before i knew all my Syncus was gone please be aware there is no official Syncus tg its a scam pic.twitter.com/hDris2Vd8k
— DaVinci.eth (@davincispace) February 26, 2024
The ERC-2612 standard supports “gas-less” transfers. So, it enables transfers for a wallet that does not hold ETH. Users do not have to approve transactions in this system. So, the trick lies in getting a user to sign a message.
Heads up, crypto fam! Unlike traditional scams, this new, sophisticated scam allows attackers to drain wallets without transaction approval.
This scam exploits the ERC-2612 token standard for "gas-less" transfers.
Here's what you need to know!👇🧵 pic.twitter.com/2BXMrvxtU4
— BrotherHood (@BHVenture) February 23, 2024
An affected user claimed that he lost $600 worth of OX tokens. The loss came after the user allegedly visited what he believed to be the official Telegram channel for the token’s developer, OPNX. However, the user suffered from a phishing scheme.
How Did it Happen?
The victim said he was asked to click an icon to connect his wallet when he first joined the Telegram group to verify that he was human. This brought up a browser window, and he opened it and connected his wallet to the website.
How it works …. The scam typically starts with phishing attempts or malicious links. Once clicked, these can install hidden software that watches for wallet activity or tricks users into signing dangerous smart contracts. pic.twitter.com/xUGjvK4blL
— BrotherHood (@BHVenture) February 23, 2024
He believed a mere connection was not a risk to his funds. However, to his surprise, all his OX tokens were gone in a few minutes. The victim said he never approved any transaction on the page. Yet, the scam was successful.
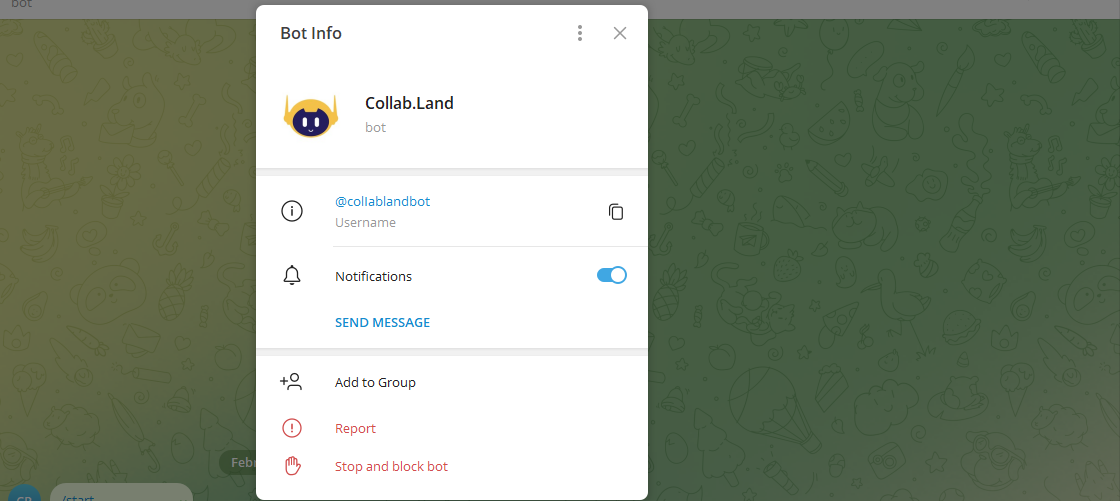
Source: Collab Land
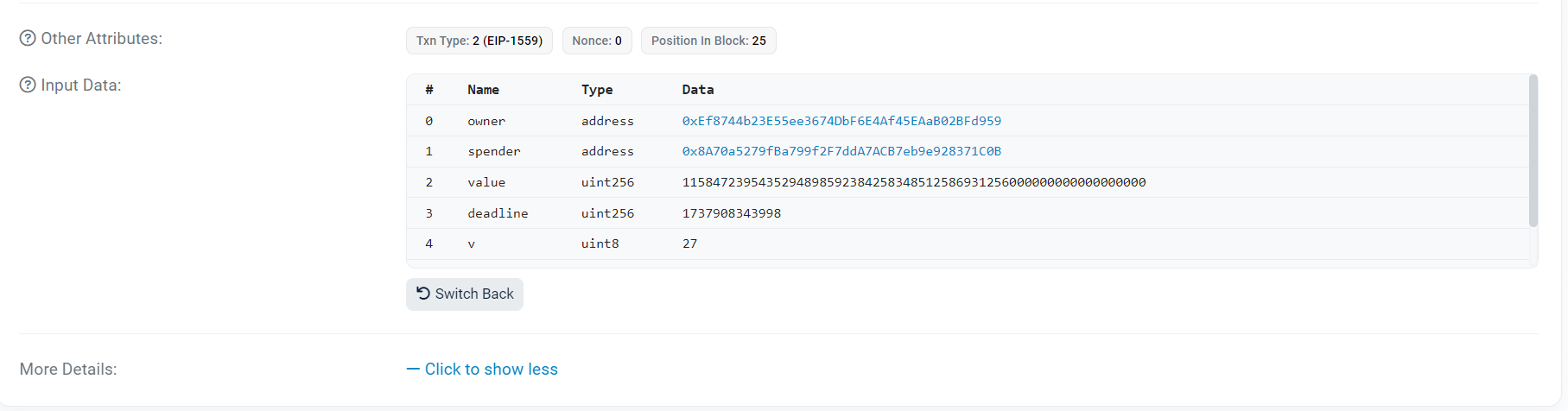
Interestingly, a visit to the Telegram group showed that it had a fake version of Telegram’s Collab.Land verification system. Blockchain data indicates that the attacker used the OX token contract’s “transferFrom” function to drain the funds. Normally, a third party can only call this feature if the user first calls “approve” via a separate transaction and specifies a spending restriction. However, there is no proof that the victim initiated such an approval.
The attacker reportedly called “Permit” on the OX token contract around an hour and forty minutes before the transfer. He marked the victim’s account as the “owner” and himself as the “spender.” The attacker also specified a “value”—the total number of tokens that could be transferred. And a “deadline,” which is the timeframe after which the permit would expire.
Conclusion
The Permit function enables a third party to transfer tokens on the owner’s behalf, but only if the owner sends a signed message granting permission. It is specified on lines 116–160 of the token contract’s ERC20.sol file.
It appears that the victim’s account was only drained because he was tricked into signing a message. The victim confirmed attempting to sign into the platform a second time. However, there was an “additional signing dialogue,” which he confirmed unsuspectingly.
In conclusion, it is important to pay extra attention when signing into sites. Ensure you are using a verified crypto platform. And report suspicious activities as early as possible.
Disclaimer
The information discussed by Altcoin Buzz is not financial advice. This is for educational, entertainment, and informational purposes only. Any information or strategies are thoughts and opinions relevant to the accepted levels of risk tolerance of the writer/reviewers and their risk tolerance may be different than yours. We are not responsible for any losses that you may incur as a result of any investments directly or indirectly related to the information provided. Bitcoin and other cryptocurrencies are high-risk investments so please do your due diligence. Copyright Altcoin Buzz Pte Ltd.